Web系统安全:第1部分 web system security: part 1 Schematic diagram of traditional encryption/decryption model (ppt) conventional encryption principles_new
2 Model of Conventional Encryption | Download Scientific Diagram
Encryption conventional simplified Conventional encryption ns2 Encryption conventional algorithms wiki diagram flow figure
Conventional encryption algorithms
Conventional encryptionWhat is the conventional encryption model?:electronics media Describe in detail about conventional encryption modelModel of conventional encryption.
Conventional encryption ns2Conventional model encryption cryptosystem What is the conventional encryption model?:electronics mediaSimplified model of symmetric encryption [24].

Conventional encryption model
Asymmetric vs symmetric encryption graphic illustrates the symmetricHttps (http + secure ) 2 model of conventional encryptionSymmetric cipher model.
The overall diagram of this encryption scheme.Mixed encryption model diagram Encryption symmetric simplifiedConventional encryption & conventional encryption model.

Model of conventional cryptosystem
Conventional encryption model in network securityComputer encryption model. Encryption symmetric asymmetric keys aes illustrates hashed encrypting definitions identicalSymmetric model encryption classical techniques cryptosystem cipher key notes generated produces plaintext message form source chapter.
Encryption model conventional cryptography symmetric algorithm key process will journal onlineKey cryptography ppt Conventional encryptionElliptic curve cryptography in blockchain : basic introduction.
Chapter 2. classical encryption techniques
Benchmark of symmetric and asymmetric encryption- using the opensslConventional encryption geeksforgeeks Crypto m1 (part-1) – telegraphConventional encryption model.
Information security page 34 (q 04) with a neat diagram explain howWhat is asymmetric encryption & how does it work? Encryption asymmetric does work data example works decryption use algorithms keys plaintext changesCryptography policy pdf.

Mod 1 > week 1 > day 4
Encryption data types methods proofpoint definition numbers use place sender between receiver importance takes prime worksSimplified model of conventional encryption .
.


What is the Conventional encryption model?:Electronics Media
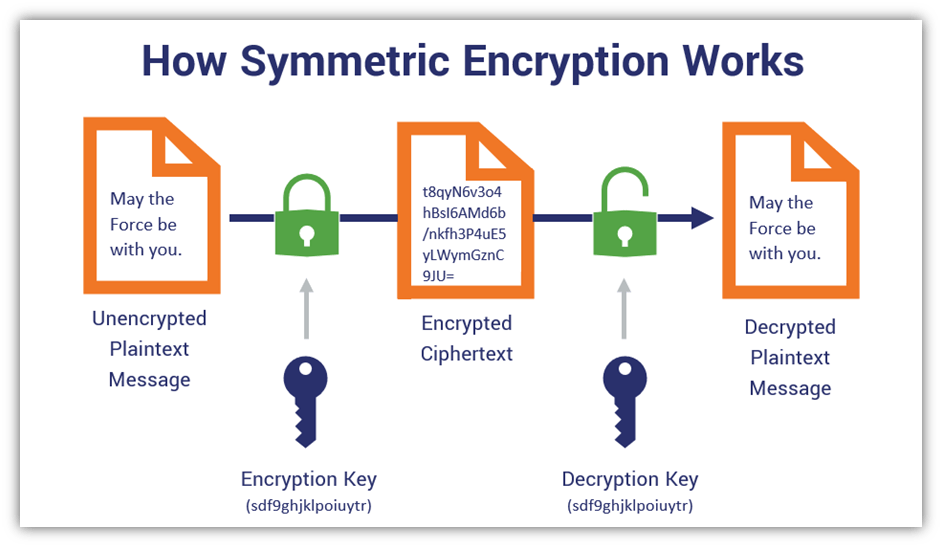
Asymmetric vs symmetric encryption graphic illustrates the symmetric

Chapter 2. Classical Encryption Techniques - Shichao's Notes

Web系统安全:第1部分 Web System Security: Part 1 - Quick博客

Describe in detail about Conventional Encryption Model - The

Conventional Encryption - GeeksforGeeks

2 Model of Conventional Encryption | Download Scientific Diagram